 I've never been comfortable with the idea of Certificate Authorities (CAs). It's always felt like a system built on a single-point-of-failure. And single-points-of-failure are anathema to secure and reliable design of any system, computer or otherwise.
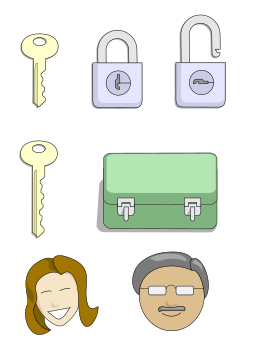
I've never been comfortable with the idea of Certificate Authorities (CAs). It's always felt like a system built on a single-point-of-failure. And single-points-of-failure are anathema to secure and reliable design of any system, computer or otherwise.Paul Venezia, a system administrator columnist for InfoWorld that I've come to respect, presents a compelling case for a sea change in our approach to online security in his September 16, 2013 column "Restore the right to privacy with self-signed certificates."
Recent revelations of security software back-doors and government collection of essentially all Internet data is finally motivating people to rethink how we do security.
But we've had 30 years of political philosophy that says government workers can't tie their shoes without the help of private business. So, any capability the government has today was developed for them by government contractors -- private businesses. And there are a lot of things more important to private businesses than the security of their client's data, especially when their clients are government agencies.
If we're worried about what the government does with our data, we should be apoplectic about what profit-seeking, completely unaccountable private businesses are doing with it.
For example... do you really think a government contractor, in fear of going out of business, but with valuable client data sitting on its computers, is not going to do everything it can to "leverage" that "asset" to save the company?
Today's browsers make it difficult to do anything other than trust the now untrustworthy CAs. Changes need to be made in the way browsers manage certificates to streamline the process for self-signing. We're not entirely dependent on the browser developers though. Experimental improvements can be made browser extensions until the mainline code can implement a robust and reliable process.
Let's get to work!
No comments :
Post a Comment